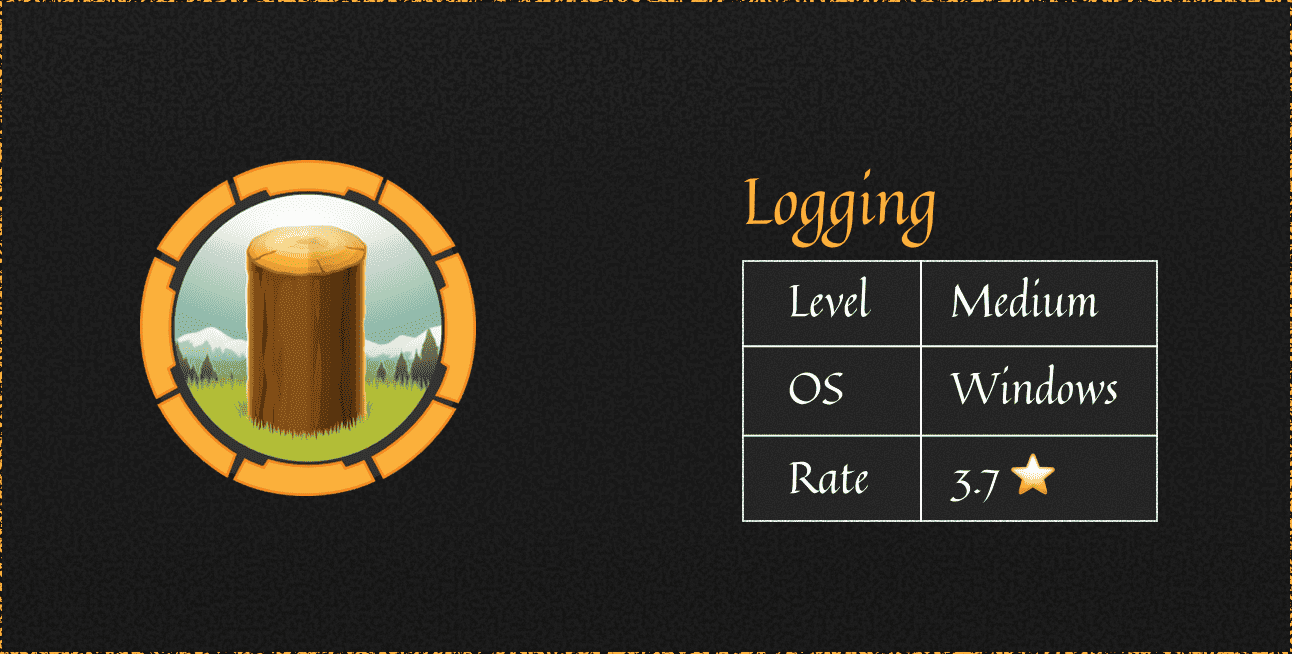
Overview
The machine starts by Simple enumeration that discovers share with leaked credentials in a log file, this account has generic write over one of the accounts so we perform Shadow attack and getting winrm to find a binary and hijack its dll to get user WSUS connection to subdomain so we poison dns record and get that connection to our fake WSUS to get shell as NT SYSTEM
Enumeration
lets start with our nmap enumeration
...