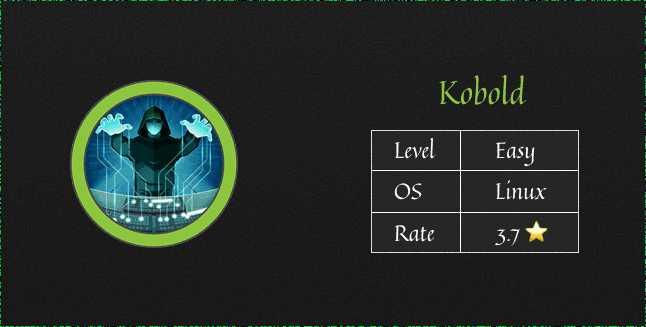
Overview
The machine starts by finding a virtual host running on 443 that hosts an MCP service that is vulnerable to RCE attack which let us get initial foothold to the system as low privileged user From here through the Privilege escalation I don't know if my way was the intended way to solve this machine so I guess we'll have to wait for the official writeup
Reading the official writeup is important because it gives you new insights that you might not have thought of
Enumeration
we are gonna start our enumeration process with nmap
...